Link to challenge: https://academy.hacking-lab.com

Date Completed: 22 December 2019
Challenge
HV19.22 The command … is lost
|
1 2 3 4 |
Introduction Santa bought this gadget when it was released in 2010. He did his own DYI project to control his sledge by serial communication over IR. Unfortunately Santa lost the source code for it and doesn't remember the command needed to send to the sledge. The only thing left is this file: thecommand7.data Santa likes to start a new DYI project with more commands in January, but first he needs to know the old command. So, now it's on you to help out Santa. |
Resource mirror: thecommand7.data
Solution
We inspect our data file and Google some of the hex sequences inside like :100000000C9435000C945D000C945D000C945D0024 and :00000001FF . We soon realise its the hex dump (or machine code) for a program for an AVR micro controller. Based on our search it seems like the dump came from the Atmel ATmega128. We decide to try and use run this hex file in some AVR emulator. As we are on windows we will try using Atmel studio which we have used before for other projects. First we replace spaces with newlines in our hex dump as this seems to allow third party tools to read the file easier.
Next we generate some Atmel ASM code from our hex file using the third party tool ReAVR:
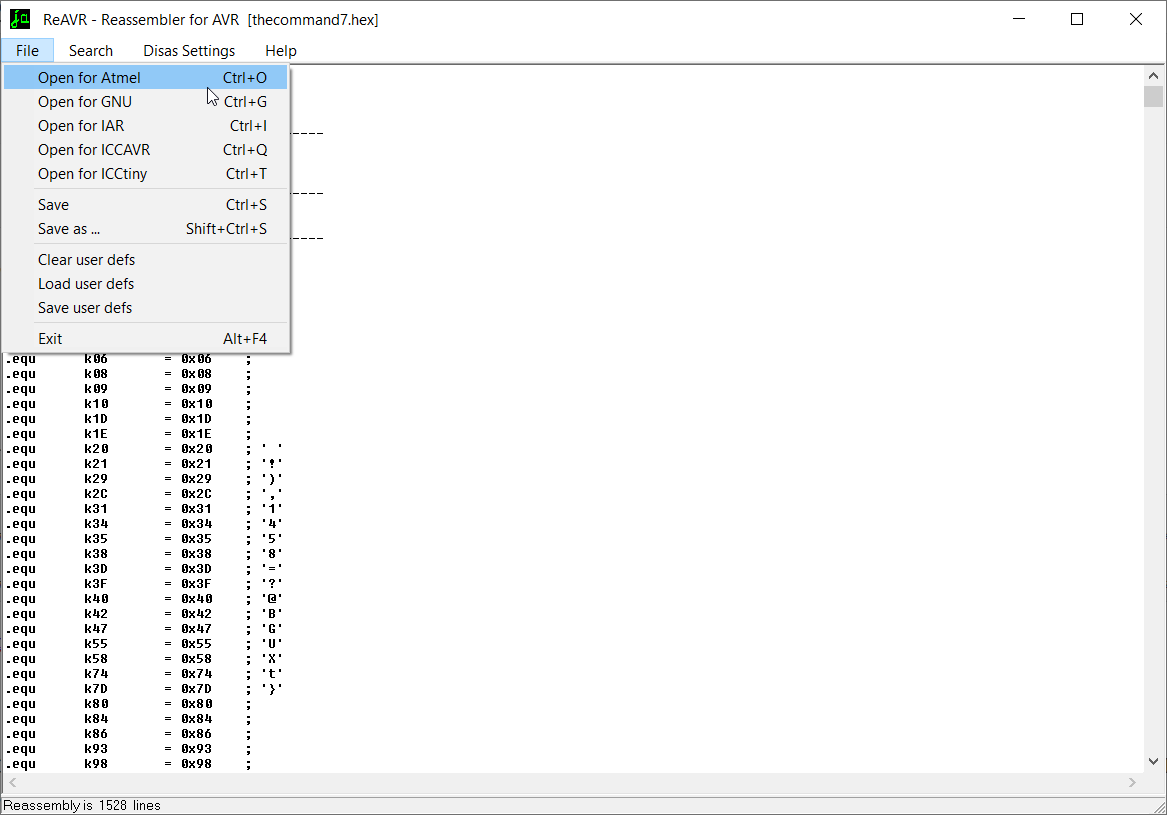
This generates some Atmel compatible ASM code which we try to run directly in Atmel Studio in an empty ASM assembler project.
We receive one error which tells us that
rcall 0x0F78 has a relative jump which is out of reach. We comment it out for now to attempt to run the program.
We let the program run in our debugger and then pause it after some time and inspect our registers in the data segment:

Thankfully, it contains our daily flag!
Flag: HV19{H3y_Sl3dg3_m33t_m3_at_th3_n3xt_c0rn3r}